Press Room
Contact
650 Castro St, Suite 120-427
Mountain View, California 94041
+1 (415) 649-5462
press@vorlonsecurity.com
Company Background
Vorlon was founded in 2022 by Amir Khayat and Amichay Spivak who hold a combined 35+ years of cybersecurity experience. Prior, they developed and sold a Security Orchestration Automation and Response platform called Demisto (now branded XSOAR) which was acquired in 2019 by Palo Alto Networks in its third largest acquisition to date.
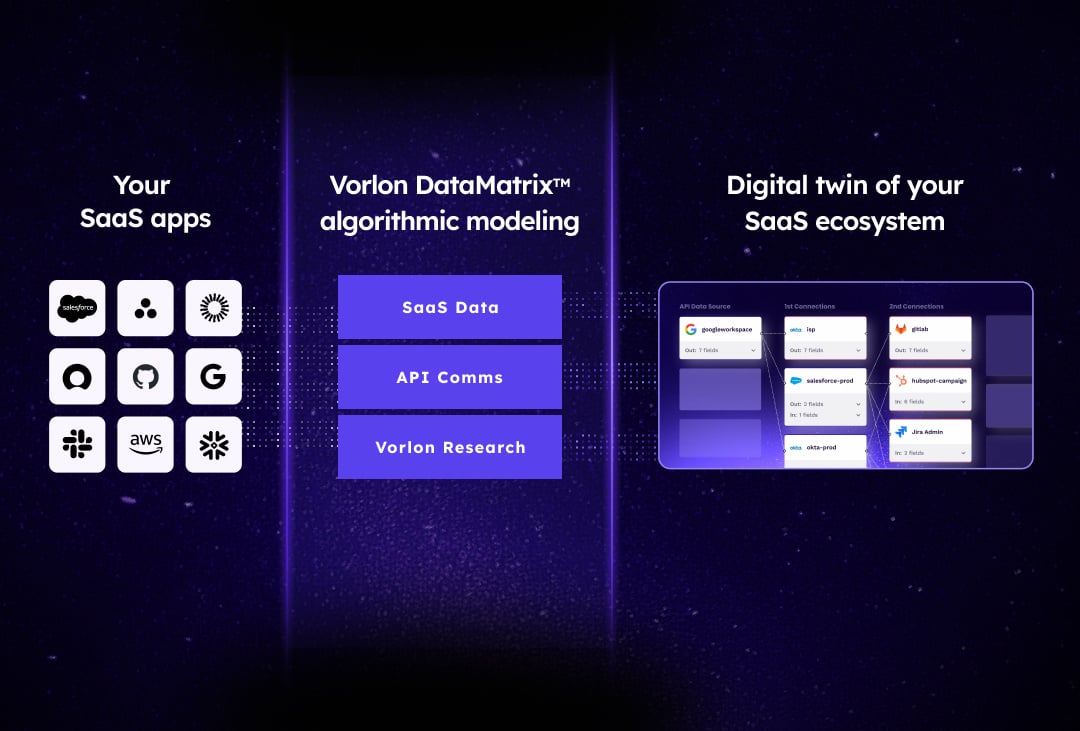
While deploying automation solutions for thousands of customers, Amir and Amichay identified a serious problem facing Enterprise organizations. With the rise of automation and continued demand for greater productivity, organizations are increasingly relying on other vendors’ (third-party) applications and services to drive efficiency within their businesses. Every vendor uses Application Programming Interfaces (APIs) to enable their own software to communicate with other systems. This communication is facilitated by ‘secrets' like OAuth, API keys, and user credentials. However, the methods used to transport these secrets continuously pose a security risk to the customer (the one consuming the APIs)—usually by granting over-permissive access to other sensitive data. And while vendors take certain precautions to secure the development of their own APIs, there has been no attention paid to protecting the data in motion from one system to the other.
Today, large enterprises consume an average of 25,500 APIs. While there aren't any good references for the number of APIs a large enterprise publishes, Google itself publishes 246—more than 100X less than what is consumed.
Oftentimes, APIs are granted more access than necessary to perform the task they are designed to do (we call this over-permissive) and the access granted to APIs are able to inadvertently access sensitive data, including Personally Identifiable Information (PII), Protected Health Information (PHI), and even Payment Card Industry (PCI) information. This sensitive data can then be exploited by threat actors in the event of a breach or leak. The APIs themselves are often exploited by threat actors as well.
In fact, 98.3% of organizations have a relationship with a third-party that has experienced a data breach in the last two years. Chances are that you or someone you know is involved in a data breach right now - but you wouldn't even know it because it takes an average of six to seven months to identify, not to mention the two to three months it takes to mitigate.
Our customers use Vorlon to detect, identify, and remediate these threats.